Airwaves Are Our Weapons
An Introduction to Software Defined Radio for Anarchists, Insurgents, and Other Rebels
Traditionally, when we have discussed wireless communications, eavesdropping, and the building of communications networks it comes along with a sense of disempowerment. It is a discussion in which we often feel like passive observers, or those subject to the actions of others without recourse. It is a discussion that often plays out in the realm of courts and legislative activity, which, as anarchists, is not the sandbox that we usually play in. The terrain of engagement itself is owned by those that are allied with the state, and which provide it easy access to our private lives on request. We often view ourselves as operating on hostile lines, within hostile networks, whether that be a social media platform or something as basic as a phone call. The resulting discourse is one that often feels distant but impactful at the same time, impossible to touch even though its implications on our lives are significant. There is almost a spectrality to communications, but one that merely haunts us. This view is not incorrect; this is our reality...now. But, as we grow and come into increasing conflict with the state our capabilities need to change, and we need to become active protagonists in this story.
Unfortunately, in anarchist circles, the discourse around technology tends to be a bit reductionistic; either technology is an indicator of a structure of domestication that is killing us all, or it is the medium of our salvation. The reality is, though, that nothing is this simple, especially the technical. Technology is everything that us humans use to supplement our physical capabilities, everything, and as a result it is not something that can simply be avoided or destroyed, if that were even preferable. At the same time technology is also bound up with the entirety of the conditions of its creation and use, the appropriation of the capability for a purpose, in this case usually profit and repression. We can see glimpses of what a more complicated posture toward technology can look if we examine early hacker scenes. In the mid-1980s there was an online community referred to as WELL (Whole Earth ‘Lectronic Link), which was run by a group of old hippies that also ran the Whole Earth Catalog. The idea behind communities like WELL was to form spaces, outside of the control of the state or corporations, where autonomy could exist in the absence of being able to overthrow capitalism in reality. A utopianism grew, incorporating things like early virtual reality, in a narrative very similar to that of LSD in the late 1960s. It is this utopianism that forms the absurdities of current Silicon Valley politics, this idea that speech is something that happens in a bubble separate from the world, the idea that everyone should have access to every asset regardless of who they are and how they interact with others (even if they are using those assets to attack people), the idea that computers and the internet are always a better solution to a problem. It is a view that naively ignores the entirety of the space outside of it.
At the same time there was a rising genre of cyberpunk literature that was starting to talk about the inverse, the ways that technology can function as a mechanism of control and the operation of political and economic power. These stories were filled with courageous underground hackers taking on the evil corporations that had bought and were destroying the world. In this narrative technology is a mechanism for standardization, the generation of automated worlds, the creation of worlds dominated by machines, in which the developers and owners of those machines become all-powerful. It is from here that a lot of the outlaw hacker mentality emerges from, and where much of the modern hacker subculture draws its roots from. The partisans of the hacker mentality eventually started breaking into systems at companies like TRW, and saw the sheer volume of data that was being kept about individual people. They invaded the WELL and started an open debate about computers and their political implications. The hackers who invaded the WELL were not arguing that technology was bad, or purely destructive, even; just that we cannot think of the technological as separate from the social, political, and economic context of its development, production, and use. This means, that for as much as it does make sense to be skeptical of the current uses of technology, the implements themselves can be turned to different uses, potentially even against the context of their production.
When discussions of technology occur in anarchist circles the tendency is to focus on implements that we are familiar with, phones, chat apps, email, and so on. On this level we are often interacting with things we consume; a cell phone, the internet, a computer, etc. This layer of interaction is one which is frequently determined, in large part, by things that we cannot, and do not, have very much control over. But, what is often missing from these discussions are the understandings and uses of lower level technologies, or technologies that exist on a level that we are able to exert control, in which there is less abstraction separating ourselves from the action we are taking. Let us take a simple example, the computer operating system. An operating system like Windows is a series of tools and layers of abstraction that allow us to operate a computer by clicking and typing things that we can read. Underlying this, though, there are numerous execution layers, from code abstractions, intermediary language environments, machine code, binary, and eventually electrons being run through magic rocks that we made think. Much of what hackers do that others think looks like magic is based on learning how to manipulate these other layers of the system, where there are less limitations, fewer abstraction layers, and a more direct relationship between the system and the user. When we get down to a lower level like this we are dealing with concepts of science and physics more than we are dealing with specific devices or machines, and those concepts can, and are, often used to manipulate systems in unintended ways. On this layer, if one can figure out how to execute the task they are trying to undertake, there are very few restrictions on what one is able to make the computer do, as long as it is logically consistent.
One of these lower layer technologies that we utilize all the time, almost constantly, that is often abstracted, but able to be directly controlled, is radio. When the term radio is used it is often to identify audio signals that travel over the air, and technically any radio signal could be heard as a sound wave, but this is a small spectrum of what radio is used for. In essence, radio waves are used everywhere, from our car dongles and garage door openers, all the way to satellite communications, the sending of data between space stations and Earth, radar, essentially anything wireless. Just for a second, stop and take a look around just the room you are in. Try to identify every wireless device you have in that space; think through what sort of data could be getting sent over the air, and what it would look like to interact with this data directly. It is sort of overwhelming, in most contexts, just how much radio functions in core elements of our lives, and this is just what we are immediately aware of. Radio is fundamentally different from many other technologies in one core way, it is almost entirely open to be used. The airwaves are artificially separated into bands by governments for the purpose of regulation. But, absent this artifice of legality, radio is able to be used by anyone to listen to or transmit anything that they are capable of figuring out how to receive or send out. It is more of a science, or a principle of physics, than a specific technology and, just as with low level computing, that gives us a lot of autonomy over how and why we use it.
With radio we can transmit data, voice, noise, random signals over hundreds of miles, using open airwaves, outside of networks controlled by our enemies. With radio we can eavesdrop on the state, and engage in signals intelligence as part of political actions. With radio we can develop our own communications protocols, devices to use those protocols, and ways to protect these signals from surveillance. In this guide we are going to discuss how to utilize radio, what equipment one would need for some simple operations, and some links out to more advanced materials for those that really want to continue to learn beyond the basics. Before getting into the practical skills involved in starting to engage with radio, let’s take a detour and talk a little bit about what radio is, and ways we can start to understand its importance.
Background and Basics
The term radio is used in a colloquial sense to mean, often, the listening to frequencies of wavelengths in the audible spectrum; AM and FM radio, family band walkie talkies, etc. The concept of radio is much broader, however, as are the possibilities for its use (and misuse). Radio refers to the use of radio waves to send information wirelessly over some space. Radio waves, in turn, are electromagnetic waves of radiated energy traveling through the air. When we turn on the radio in a car (if anyone still uses analog radio in their car…) what is occurring is that the antenna on your car, which is just a metal pole with a wire running through it, is literally coming into physical contact with one of these waves. That wave is then sent as energy down the wire to the actual receiver, resulting in us hearing sound.
Just as a thought exercise, real quick, if we assume that radio signals, even for a single FM station, need to be present everywhere in order to be received, just start to think about how dense the airwaves are with signals. We have remote controls, car door lock systems, audible radio, radio frequencies used just to send things like satellite data, military communications, analog television, etc. The air around us is constantly saturated with these signals. Now, what is really amazing, and slightly dangerous, about radio is that any of these signals could be intercepted, made sense of (in the absence of encryption), or even broadcast. Just think of all of the possibilities!
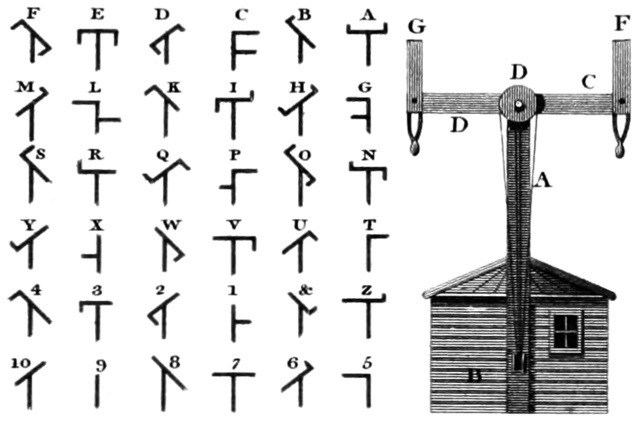
The roots of radio and wireless transmission can be traced back to attempting to solve for the limitations of physical lines in the telegraph system, but the roots of the telegraph system trace back even further. The first high-speed long range communications systems were semaphore or optical telegraphs set up by Napoleonic armies to relay messages over long distances in short periods of time. The system consisted of these towers, spaced out 5-10 miles apart, which had flappable arms controlled from inside the tower. The pattern that the arms were in indicated a letter, and using this system messages could be sent over hundreds of miles in a couple of hours; a massive advantage in the military operations of the time.
Starting in the 1840s we started seeing the introduction of the electric telegraph. Using devices that you would need to crank to in order to generate power, it was possible to send messages over hundreds of miles almost instantly, by the comparative standards of the day. The early telegraph system was standardized in 1865 with the introduction of Morse Code. This system had two advantages over its optical precursors; it was not visible by the enemy, and messages could get sent more quickly. This came at the cost, however, of the laying down of an entire infrastructural lattice to support this new wired system, which was expensive and prone to failure.
In the 1870’s James Clerk Maxwell developed the theory of electromagnetism, that it is possible for energy to travel over the air; prior to this all wavelengths were thought to be visible. The first radio waves were generated in a lab in 1886, quickly followed by Guglielmo Marconi building the first full radio system, which used a transmitter to send Morse Code to a receiver. By 1901 that signal was able to travel across the Atlantic Ocean, and by 1905 we started to see the rise of antenna technology, and the building of different types of antennas for different purposes. For the first couple of decades of modern radio all signals were intermittent, namely they sent pulses of electricity over the air, as we see with Morse Code messages. What most of us understand as radio today, the sending of audio in a constant stream, emerged during World War I with the advent of AM (amplitude modulation) radio, and the first commercial radio broadcast was sent out by Westinghouse on November 2, 1920.
With the advent of continuously broadcasting radio signals, communications changed forever, with messages being able to be sent in near real-time across large distances, reliably, and with full audio capabilities. A full discussion could now occur wirelessly, and one of the first places that change was felt was in the military. When militaries adopted radio technology it became possible to project force globally, keep vastly dispersed forces in communication, and organize logistics over thousands of miles. The use of radio created a problem however. Unlike telegraph lines, which would need to be manually tapped in order to intercept messages, radio signals could just be grabbed out of the air with the right equipment, giving birth to both modern communications security and the use of signals intelligence; giving birth to modern cryptography and ultimately the computer.
There is definitely a lot more history that we could review here. If you want to take a closer look into this history, see the resource guide at the end of this pamphlet.
On a technical level, radio broadcasts exist across a wide spectrum of signals referred to as the RF spectrum (the Radio Frequency Spectrum). These signals are measured in hertz, which measure the number of frequency cycles one could receive in one second. Often, when we come into contact with hertz, it is in the form of megahertz (MHz) or gigahertz (GHz). The radio spectrum is regulated, in the US, by the Federal Communications Commission, which regulates all communications infrastructure. The FCC has divided the radio spectrum up into different groupings of frequencies. For example Project 25 (P25) digital trunked radio systems (which we will get into more later) are used widely by police in the US, and those signals can be found between 136-174 MHz, 403-512 MHz, and 746-806 MHz. Every type of radio signal, from satellite communications all the way down to the Bluetooth headset connected to your phone is allocated some range within the overall radio frequency spectrum. A visual graph laying out all of the different bands and what they are allocated to can be found at https://www.ntia.doc.gov/files/ntia/publications/2003-allochrt.pdf. In other regions of the world these allocations will likely look similar, but may differ slightly.
Within the US the airwaves are considered public property, but are regulated, divided up, and sold by the FCC, functionally privatizing large amounts of the spectrum. There are some open bands, where it is legal to both transmit and receive, such as the Family Band that a lot of walkie talkies and baby monitors operate in, which is between 462 and 467 MHz. Most of the RF spectrum is able to be listened to without any sort of approval or licensing. Broadcasting, on the other hand,is heavily regulated, with various licensing exams provided by the FCC to obtain different levels of certification. The reality is, though, that the FCC has incredibly limited enforcement capacity, often only taking less than 5 enforcement actions in a year, most of which are violations of rules by licensed broadcasters, and not about illegal broadcasting.
Though regulated and policed, the RF spectrum is relatively open to explore, and all sorts of information can be found this way. In this guide we are going to talk about getting set up, capturing basic signals, demodulating ADS-B signals (which identify the type, altitude, and speed of aircraft), and intercepting emergency radio in your local area. We have an entire world out there, full of information, (much of it is very useful for political resistance), and all we have to do is reach out and pluck it out of the air.
Getting Started with Software Defined Radio
A lot of this all sounds very complicated, and most sources for information that one can find about traditional radio are obtuse and filled with craft language. Radio communities are largely made up of people that are highly technical, and who often have some electrical engineering knowledge. As a result they tend to be a bit closed, and often have informal gatekeeping structures in place, so information can be hard to find. Personally, it took a few years of focused learning and messing with radio signals to feel like I had a grasp on this, and most of that was spent just trying to find the type of information presented here.
This exclusivity of radio communities is exacerbated by the fact that traditional hardware radio setups often involve massive antennas, thousands of dollars in obscure equipment, and an entire workbench to set up on.
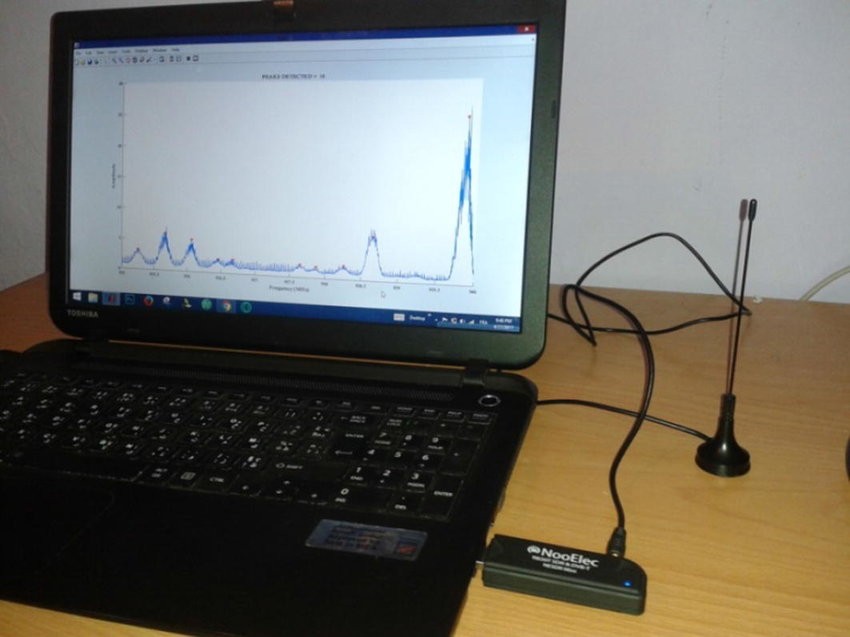
Today, however, we are able to start learning about radio in a much simpler and cheaper way, through software defined radio. Software defined radio refers to the use of software configurations to modify what signals are received and transmitted by a piece of simple hardware, as opposed to intimidating looking hardware with a bunch of knobs. Software defined radio first emerged in the mid-1970s, in US military adjacent research programs. In this guide we are mostly going to be dealing with a subset of SDR, the RTL-SDR. The term RTL-SDR is a reference to the type of signals processing chip used on the board. Around a decade ago security researchers discovered that it was possible to access raw signal data on devices that were used to receive digital TV; the chip is called the RTL2832U. Unlike traditional radio setups RTL-SDR setups usually consist of a laptop, open source tuning software, a USB dongle and a small antenna. Using this equipment it is possible to receive signals, depending on the specific chip used, between 24 MHz and 1766 MHz, a relatively wide swath of the RF spectrum.
The equipment is very cheap, often under $30, and it can be used with almost any computer. There is much more advanced and expensive hardware, with the ability to receive a larger amount of signals and often transmission capabilities. However, for what we are going to discuss in this guide, a simple RTL-SDR is sufficient.
Setup
The purpose of learning to use software defined radio is so we can have direct control over what we are listening to, and what we do with those signals. That means that we are going to need to set up a listening post of our very own!
To set up a listening post you will need the following:
Computer:
SDR relies on a separate computer to process the data that is being received. The computer should preferably run Windows or Linux. Depending on what sort of interception you want to do, the computer could require up to 4 processor cores and 8 GB of RAM, with the preference being a system from the last 7-8 years. In projects we work on locally we usually are able to get by with a cheap used Thinkpad or an old gaming PC from a friend’s closet, as long as we are only using the system for radio.
RTL- SDR Dongle:
There are a lot of variants of RTL-SDR dongles available, mostly online. These will range in quality from bootleg copies of working devices all the way up to dongles that can cost a couple hundred dollars. For our purposes all we need is a cheap RTL-SDR of good quality. We would suggest either getting the RTL-SDR Blog dongles (which is what we use) or something from NooElec, a company that makes consumer grade SDR hardware. Both are very capable devices for the price.
USB Extension Cable:
A computer motherboard throws off a lot of electromagnetic interference, and that can negatively impact the ability to receive signals clearly. A USB extension cable three feet in length or more will be sufficient to distance the receiver from the computer.
Software:
There is a lot of software out there, and we will be discussing some of these frameworks as we go. But, to just get started it is recommended that you download SDR#, if you are using Windows, or GQRX, if you are using Linux. Both frameworks are very capable, and can be used for a lot of different types of interception, but are also easy to use, free, and open source. Depending on the system you may need to install drivers as well. Follow instructions on https://www.rtl-sdr.com/rtl-sdr-quick-start-guide/ for more information and troubleshooting.
A Good Listening Position:
This is sometimes the hardest part of setting a system like this up. The ambient environment is full of other signals, electromagnetic waves, power lines, brick walls, and any number of other sources of interference; this is especially true for those of us in cities. It is definitely possible to receive signals using a computer on the ground floor of a building, in the middle of a room, but are likely to get far better reception if listening from a location that has limited interference. In the past we have set up listening posts in more rural areas on the edge of the city, as well as positioned listening posts on the third or fourth floor of a building, above the power lines. Generally, due to local police repression, we tend to keep antennas indoors and not visible from the outside of the building, but if that is not a concern, setting up antennas on a roof is the best option.
A Solid Group of People:
Listening to radio for hours on end can get tedious. Most of the time you are just sweeping ranges that do not have much going on, or it is a firehose of information, like a police scanner. Either way, it is important to take breaks. This sort of activity does take some work to learn and get comfortable with, so finding a group of people that is trusted, and that is interested in radio, is crucial.
The First Leap Into DIY Signals Intelligence
In government circles the interception of radio signals is referred to as Signals Intelligence, or SIGINT. For much of the history of radio the ability to intercept signals, the technical knowledge to demodulate them and make them useful, and the sheer volume and cost of equipment meant that mostly states were able to pluck signals out of the air for information gathering purposes. With the advent of consumer grade SDR, however, this is a capability that is not only possible, but has been used in actions to keep people safe, out of jail, and effective.
As was discussed earlier, the number of signals that are traveling through the air at any one point is immense, most of which are not able to just be listened to as coherent audio. There are some signals, however, that are very easy to pick up, and this is where we will start. After getting everything set up, plugged in, and turned on, it is possible to start intercepting signals immediately. To begin to learn it is recommended that you work on picking up NOAA weather radio broadcasts (162.400 – 162.550 MHz), two way radios (462.5625-462.7250 MHz), and local AM and FM stations. These signals are easy to receive, are intended for open public use, and can help you get comfortable with using SDR. NOAA weather alert radio sounds like the recordings accessible at the link below.
https://archive.org/details/NOAAWeatherRadioWXL40/AMACLINWR.mp3
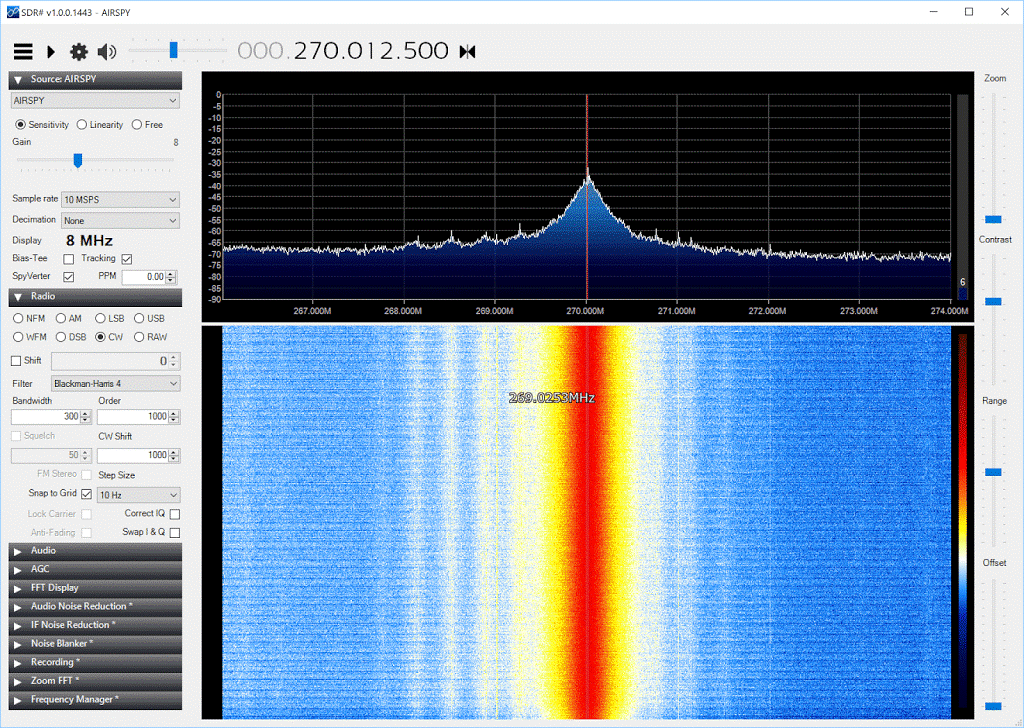
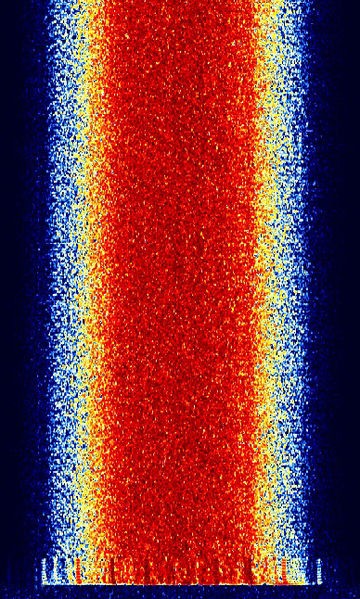
When you fire the system up, and start the software, you will likely be met with a waterfall graph. A waterfall graph is a visualization of the signals within a specific group of frequencies. The below image is from SDR#, but GQRX will display similarly.
Now, with this basic setup we would only be able to listen to signals. Most of what we will hear is going to sound like robots chattering; that is data being sent over the airwaves. It sounds like this:
https://www.sigidwiki.com/wiki/Category:Trunked_Radio
The demodulation process involves extracting this data, in a usable form, from these captured transmissions. For example, and we will discuss this more later, if you try to tune to the control channel of digital police radio system, you are only going to hear this chattering. What is being sent over those frequencies are not audible, but is data used by the radio system itself to allocate channels for discussions, which often jump frequencies mid-way through a transmission. So, for something like police radio just getting audio signals is not good enough, we have to process those signals into data that makes sense.
There are advanced frameworks, like GNURadio, which are built to allow for users to customize listeners to demodulate different types of signals. A framework like GNURadio is beyond the scope of a simple introduction though. Rather, we are going to use pre-built open source tools for the signals that we are going to intercept in this guide.
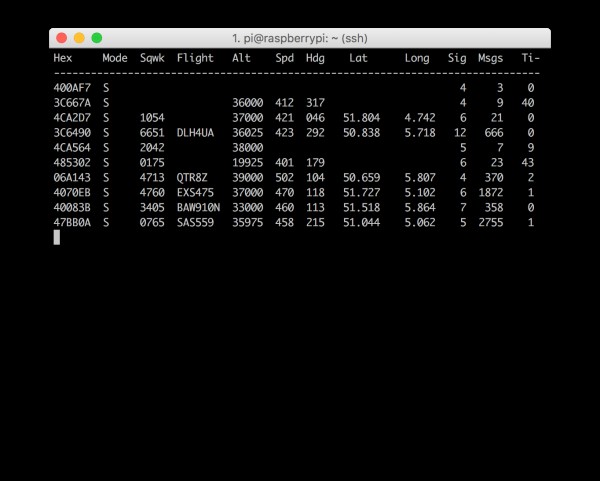
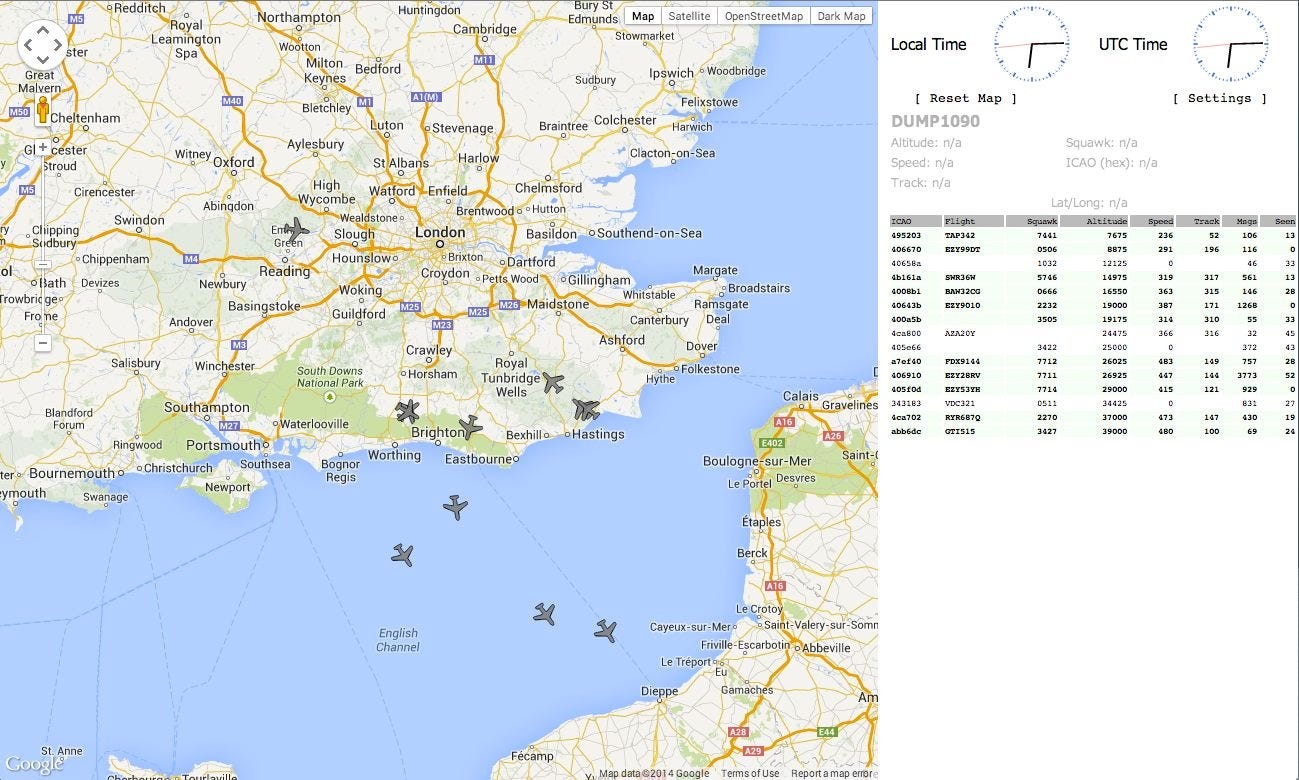
To start gathering useful data, and making sense of it, we can start with ADS-B signals. The ADS-B system is a radio specification used in aircraft to report type of aircraft, callsign, altitude, speed, and location to airports and other landing areas, and it broadcasts on 1090 MHz. In the US only airplanes are required to transmit ADS-B signals, but increasingly helicopters are broadcasting these signals. We have used ADS-B to track police helicopters in the middle of actions, especially when there is dispersed actions, and to locate staging areas for times when the National Guard comes to town (based on where a lot of cargo planes were landing in a short period of time). To get a glimpse of what ADS-B signals provide you can go to ADS-B Exchange, which is a service that aggregates the ADS-B data from thousands of SDRs around the world, providing near global coverage of every aircraft in the sky globally at any one time. A similar system also exists for watercraft, called AIS, which can be used in similar ways.
To pick up and map out ADS-B data there are a number of different possible pieces of software that you could use, but for the purposes of this guide we are going to focus on dump1090, which is the basis for most of the other ADS-B receiving frameworks.
To download and install dump1090 you can find a version for Windows at https://github.com/gvanem/Dump1090 and for Linux, https://github.com/MalcolmRobb/dump1090
Once installed these frameworks will identify the SDR dongle, tune it to 1090 MHz, start capturing data, and mapping it. When receiving ADS-B data, the demodulated packets of data contain information that looks like this:
When launched in webserver mode you will be able to access a visual map that looks like this:
If you want an interesting follow-up project, here are some instructions about how you can intercept and display NOAA weather satellite images in real time:
https://www.rtl-sdr.com/wp-content/uploads/2022/08/NOAA-Satellite-Tracking-and-Decoding-Guide-V2.pdf
With just some simple software, a little bit of time, and a small amount of resources we have been able to explore the audible areas of the RF spectrum, as well as to start mining the airwaves for signals. It only gets more interesting from here!
An Amateur’s Guide to Spying on Cops
So far, we discussed known signals that have already been extensively researched and are able to be easily utilized. We can find the frequency, tune our radio, and start listening to whatever is coming over the air. In the past police radio worked just like any other radio system, they used predetermined “channels”, which corresponded to different frequencies, and all we needed to do was tune our radio to one of those frequencies and listen to the cops plotting how to occupy our lives.
There are plenty of online sources for existing streaming police scanners. These are wonderful resources, and we can often get apps to stream them on our phones, which is helpful during actions. But, we do not control these radios, cannot tune them, and cannot prevent them from being taken down. In the past streams have been shut down by police order, overloaded with listeners, or are just tuned to talkgroups that are not relevant. To get the most relevant, most useful, information we need to build our own.
This involves more than it did in the past, where it was sufficient to just buy the proper equipment and start scanning the spectrum. Today, if you were trying to listen into police radio by manually tuning to frequencies, you may catch a small blip of a discussion, and that is if you’re lucky. Most police departments, and every department in a medium to large city, have radio systems that are digital and “trunked”. This guide will be focused on a specification called Project 25, or P25. In a European context emergency radios tend to use a specification called TETRA (Terrestrial Trunked Radio).
Digital refers to the sending of data in binary, as opposed to sending an audible radio stream. To say a system is “trunked” imples a couple of things. The first element is that a bank of frequencies is allocated which can be used to host calls. The second element is a control system which takes in transmissions, allocates them a frequency, and then send that data to all other radios in the same “talkgroup”. Not only does this mean that calls can be allocated to any of a number of frequencies unpredictably, but these systems often “jump” calls in the middle of a transmission to a completely different frequency.
This not only creates the problem of finding a transmission, but we also need to know how to follow the transmission when it jumps frequencies. Unlike “normal” single frequency radio, it is not enough to tune to the frequency that we want to listen in on. Rather, we need to figure out how to tap into the data stream that allocates channels and transmits channel information to radios. To do this we are going to tune our radios to what is called a “control channel”, or the channel that allocates calls to frequencies.
Information about trunked radio systems, their control channels, and talkgroups is widely available online. Using this information, we can begin the process of capturing emergency radio transmissions. Once you identify a control channel frequency in our area, turn on our radio, and tune to the control channel frequencies, you will likely see a signal waterfall that looks like the below image.
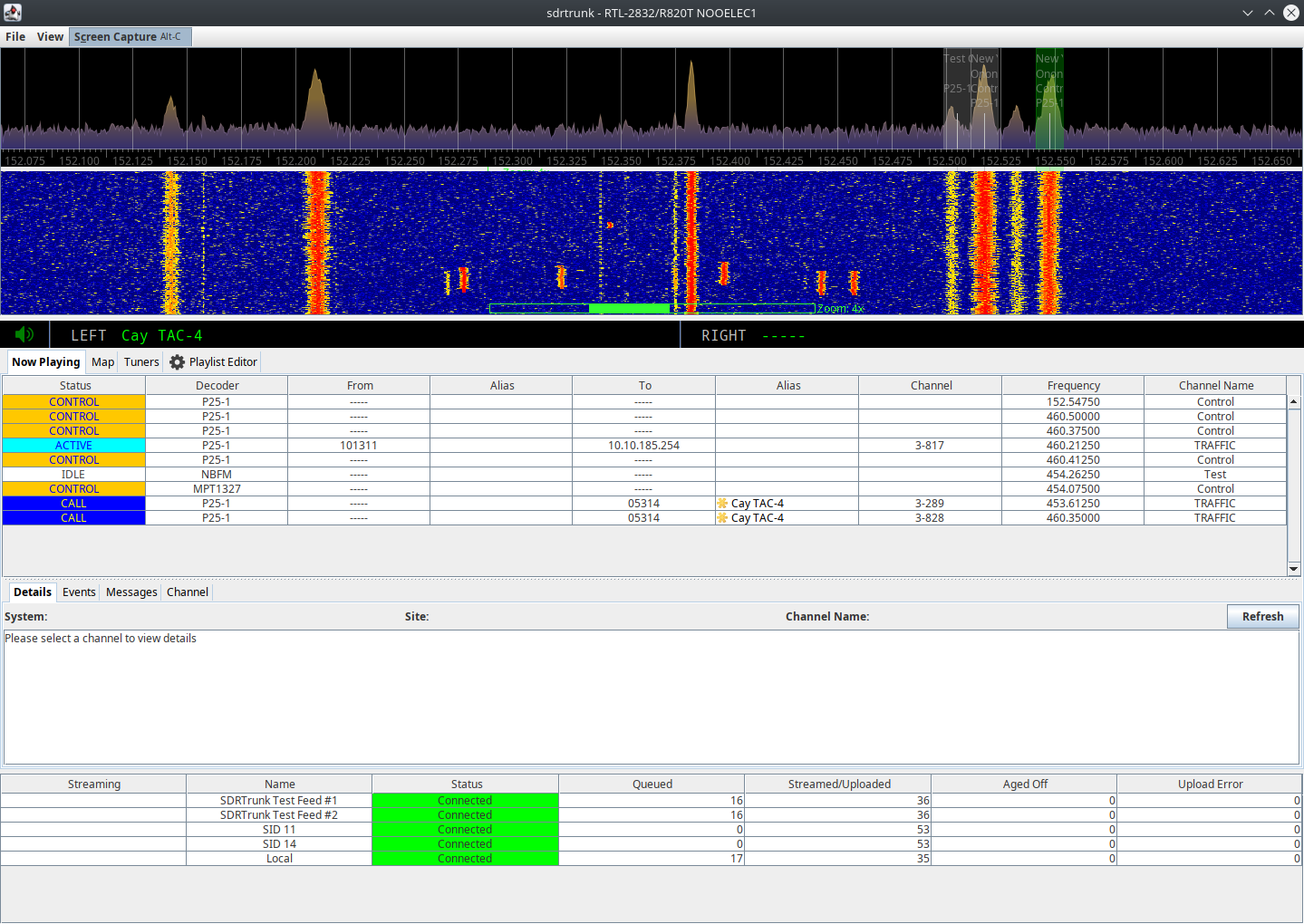
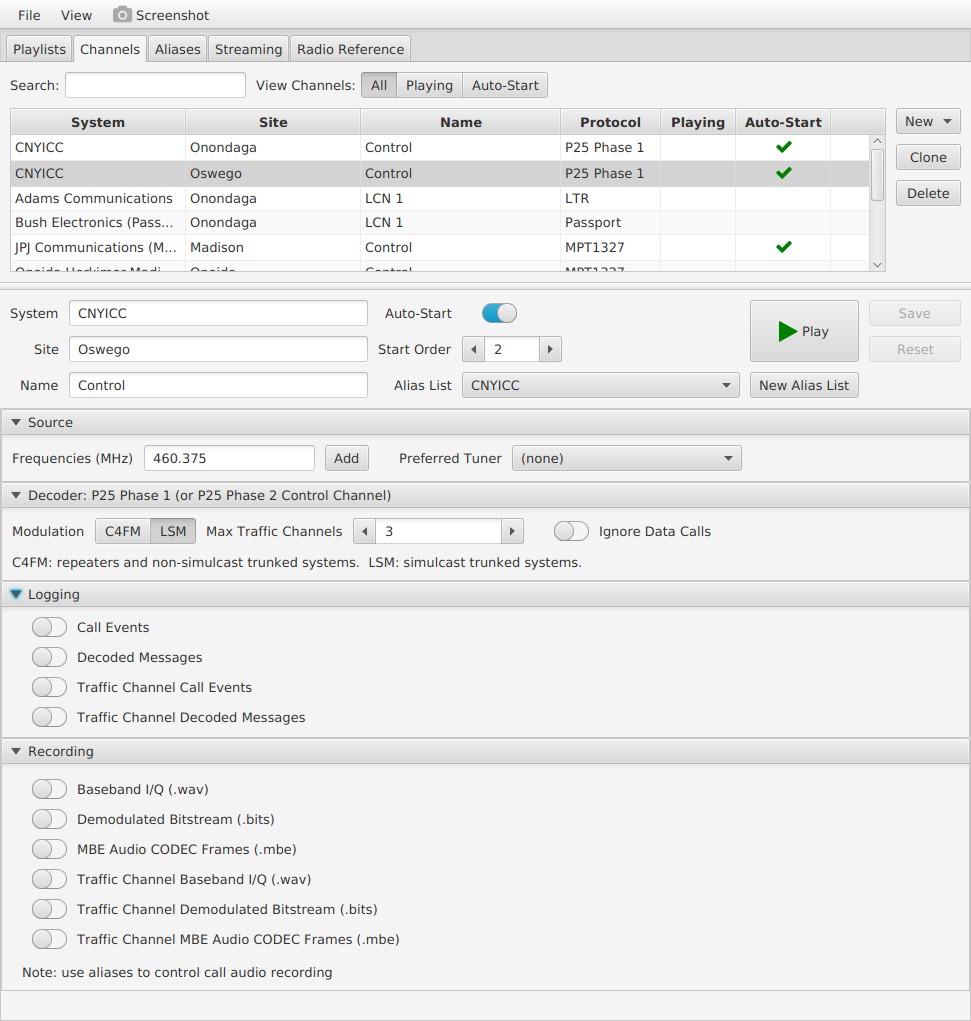
Now, of course, this is not particularly helpful. We need software to help us follow the control channel transmissions, tune the radio to the proper frequency automatically, and translate (demodulate) the signal into something we can hear. When building custom police scanners locally we rely, generally, on a small series of open source tools, depending on the objective. If the goal is to capture individual discussions, listen to them live (or stream them to listeners), and be able to prioritize what signals the radio will tune to, then the primary tool we use is called sdrtrunk, which can be found here:
https://github.com/DSheirer/sdrtrunk
The installation and setup of sdrtrunk is outside of the scope of this guide. The user guide provided at the link above is very comprehensive. Instead, we are going to skip the installation step and move directly into how it is used. Just like any SDR framework you can just plug in the radio dongle, flip the software listener on, and start tuning.
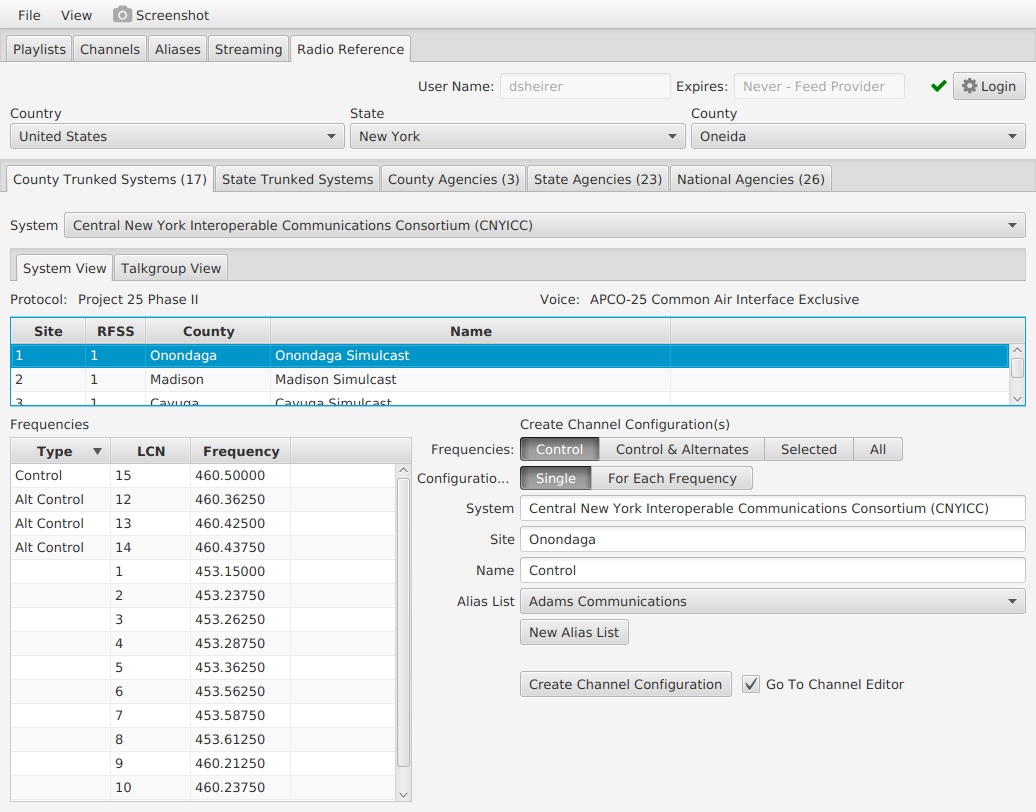
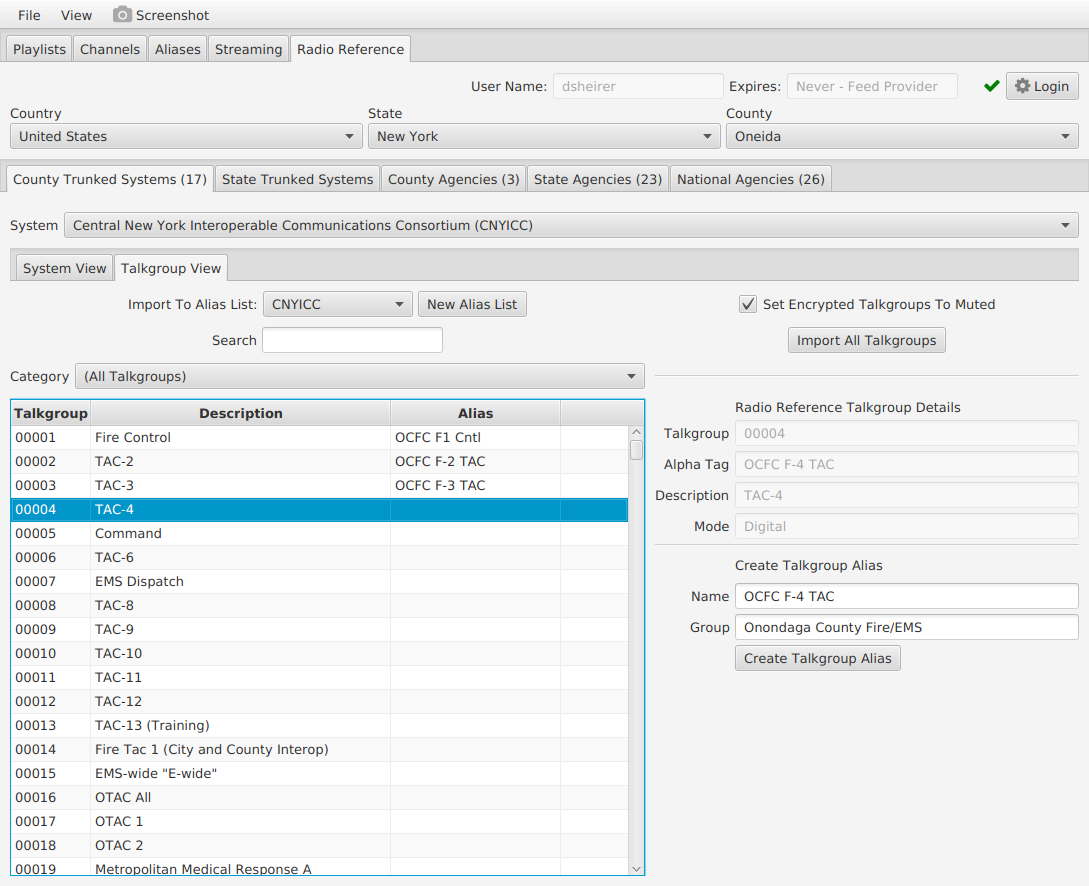
The real advantage of sdrtrunk is the ability to ingest information about a radio system, and to use that data to assist in how to tune your own custom system. To start someone in your crew, or someone you know, is going to need to know where to get information about the local emergency radio system. There are different places to find this, but the most updated information can be downloaded from https://radioreference.com with an account. This site is the most comprehensive location for technical data on radio systems of all types in the US. In the configuration of sdrtrunk there is a tool that allows you to log into RadioReference, and automatically download the information of any system you are interested in.
When you open up sdrtrunk, you will see the following screen.
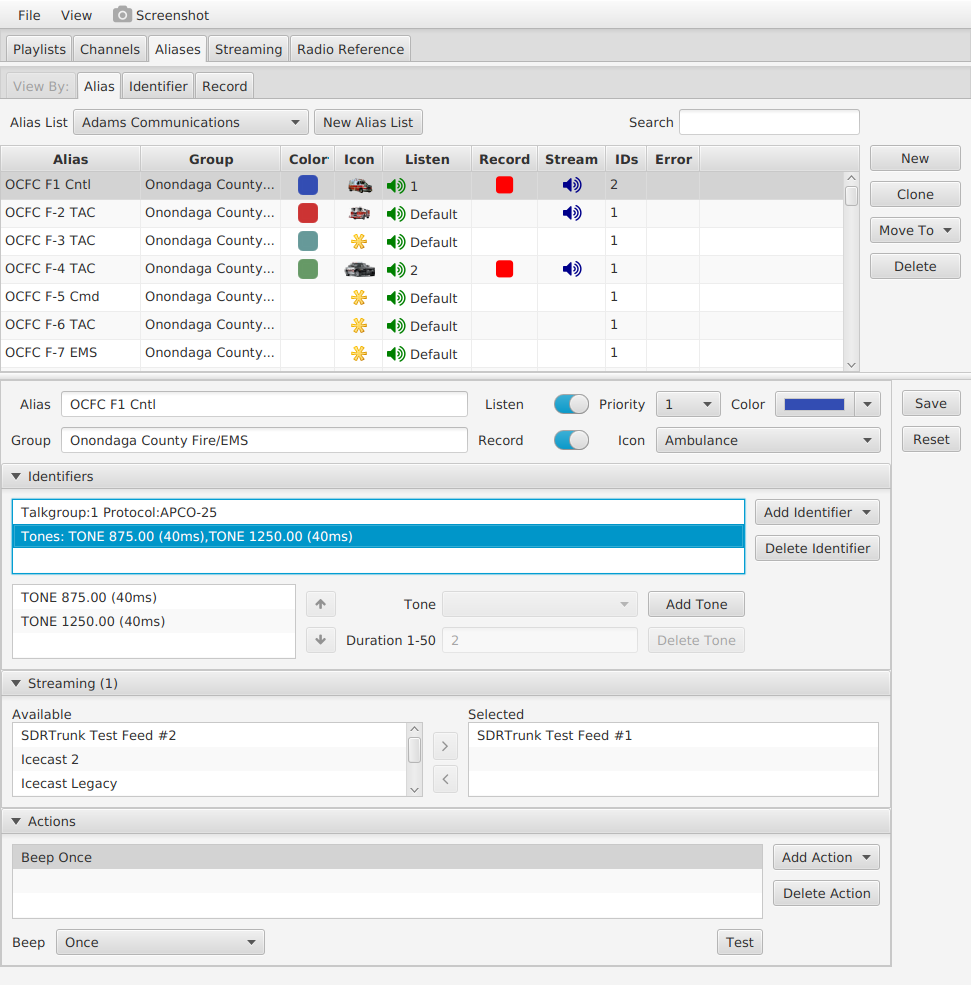
We can configure our scanner by clicking on the Playlist Editor. From there, if you have access to a Radio Reference account (and every scene should have access to at least one), you can use the interface to easily download all of your local police departments' radio talkgroup configurations.
In the section of this page that appears when you click the Talkgroup View button, we can take the data that was imported, look at the talkgroups present on the system, and import them into a “channel” configuration. A talkgroup is a user group on the digital radio system comprised of a number of radios, and all radios in any specific talkgroup can receive and transmit to any other radio in that talkgroup. The talkgroup is used as a way to divide up the overall radio system, as opposed to frequencies, with talkgroups being allocated frequencies when calls occur.
Importing the talkgroups will result in a “channel” being created, which we can now customize. We do this by selecting which talkgroups we want to listen to, which we want to mute, and what priority we want to assign to calls if more than one is being processed at a time.
After talkgroups are configured the stream can be started by going to Channels, selecting the channel you want to listen to, and hitting Start.
Sdrtrunk will then do a lot of the hard work of tracking the control channel, demodulating the signal, and tuning the radio to calls as they jump around the radio spectrum. This allows us to spend time configuring the system and listening in.
Additionally, if you would like to set up an audio streaming server (we use Icecast), you can stream the audio from your scanner to an online accessible audio stream so you can access it anywhere (including from within the middle of the protest or action).
These tools, in personal experience, have been the difference between successful disruption of urban spaces with no arrests and getting everyone rounded up in an alleyway. Being able to have advanced knowledge of preparations and the activities of the state can be the difference between victory and a jail cell.
Conclusion
With the advent of software defined radio what used to be a complex and expensive undertaking, involving thousands of dollars of equipment and years of training, has been drastically simplified. Now, with access to ample information available online on the use of SDR for intercepting various signals, the barrier to entry for setting up our own mechanisms for gathering signals intelligence has lowered to the point where it is within the reach of most anarchist communities (and if you don’t have the skills locally, ask around, someone will).
This is just scratching the surface though. Around the US organizations like Signals Rising and others are encouraging radicals to get their radio licenses and to develop skills. Once we develop understanding of how radio works, we can start to apply those principles to anything. For example, anarchists in the US are working diligently on building meshnet based encrypted communications networks, long range radio links, and mechanisms to securely communicate across vast distances in a situation where normal channels are not able to be trusted, or if a disaster strikes.
When we control the airwaves we control the means of our communication. We are able to rip networking out of the hands of the state and massive telecommunications companies, and can start to build the networks that not only allow us to fight, but allow us to build a new way of living as a part of that struggle. This is an essential shift in an anarchist movement that is transitioning from being a protest based activist movement to one that is starting to enter into more acute resistance.
Additional Sources
Map of FCC Enforcement Actions https://www.fcc.gov/reports-research/maps/fcc-enforcement-actions-against-pirate-radio-location/
Information on FCC applications, technical schematics, etc https://fcc.io
RTL-SDR Blog Quick Start Guide https://www.rtl-sdr.com/rtl-sdr-quick-start-guide/
ADS-B Exchange https://www.adsbexchange.com/
Twente University WebSDR http://websdr.ewi.utwente.nl:8901/
Priyom (collection of number stations and other government broadcasts) https://priyom.org/
Signals Identification Wiki https://www.sigidwiki.com/
Radio Reference https://radioreference.com
Google Patents https://patents.google.com
Problems With P25 Radio Encryption https://www.usenix.org/legacy/events/sec11/tech/full_papers/Clark.pdf
Directory of Online SDR Receivers https://www.receiverbook.de/